When migrating or provisioning a new workload on your Azure cloud, you must be aware that your new cloud workload has different playing roles. Central security management, authentication and security hardening must be your priority.
In this blog post, I will take you through the steps to join your Linux workload to the Azure Active Directory services. I can assure you that the steps we will go through are very simple; I will share with you the steps I went through to accomplish the same results in my lab. It took me some time to go through the many Microsoft documents to learn and troubleshoot the many issues I faced. This blog post is a summary of what I learned.
You will need the following items to join your Linux workload to your Azure Active Directory:
- Azure Subscription
- Azure AD
- Custom Domain – verified
- New account join to the new custom domain
Now, let us run through the steps we will discuss in this blog post:
- Deploy Azure Active Directory Services
- Setup ADDS DNS on vNet
- Deploy and prepare Linux VM
- Join the Domain
So let’s get started with:
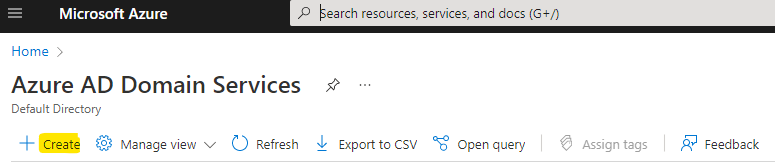
Deploy Azure Active Directory Services
Instead of deploying a Windows server and promoting to a domain controller, Microsoft Azure offers Active Directory Domain Services (Domain as a service) to help you provide domain join, group policy, LDAP and Kerberos/NTLM authentication services without the complexity of managing your own domain controller.
Deploying ADDS can be accomplished by typing Azure Active Directory Domain Services and then pressing “Create”
Fill in the required details. Here is an example of the responses in my lab:
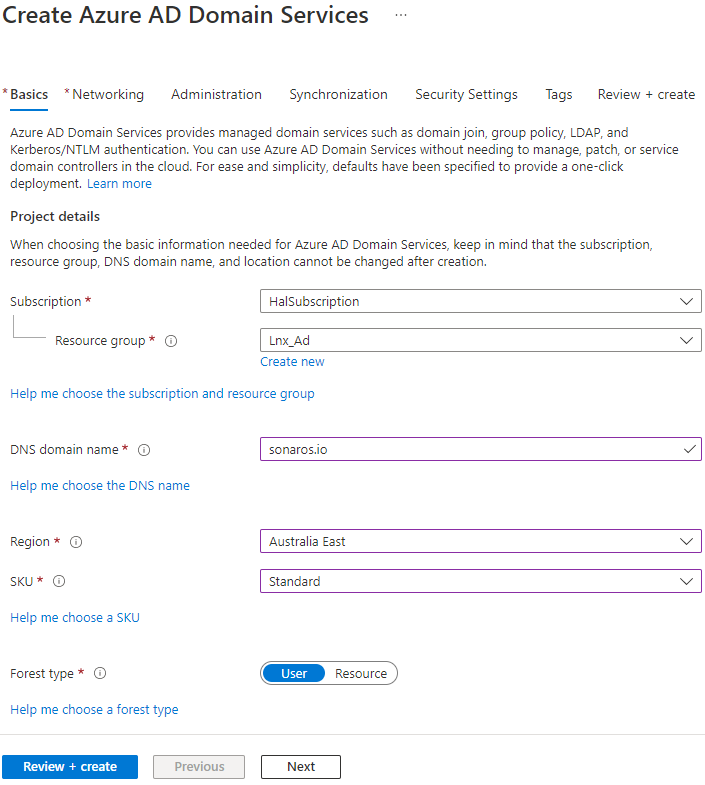
Please note that I used a custom domain name Sonaros.io and the SKU: standart. I have shown below the remainder of the screens, provided here for reference:
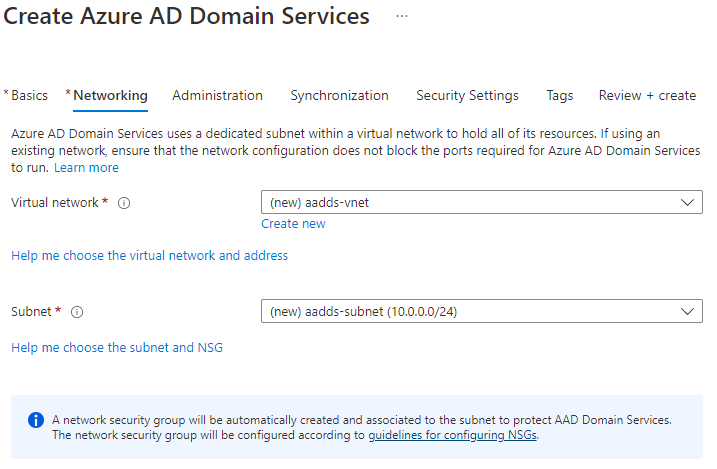
Networking – keep the defaults:
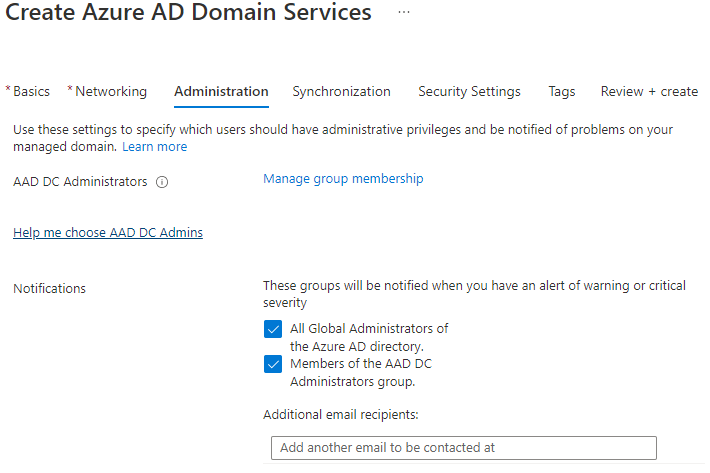
Administration – Include any accounts from your custom domain under AAD DC Administrators
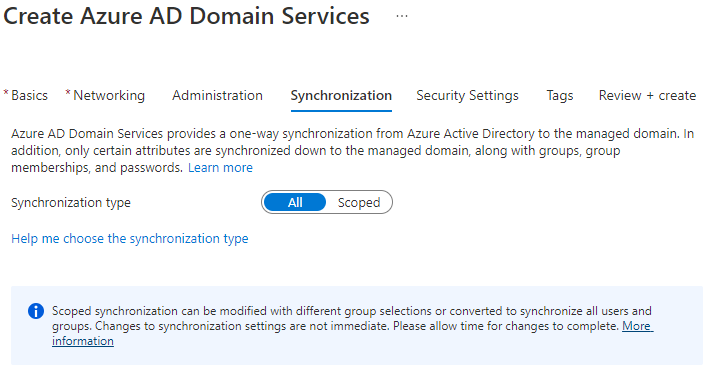
Synchronization – All
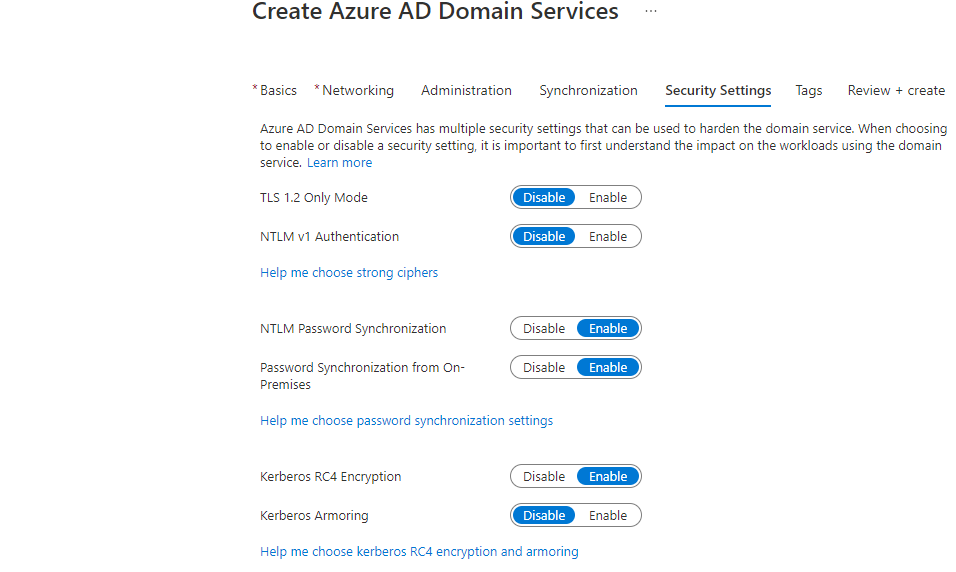
Security Setting – Defaults
Now we are are ready to press Review and Create.
Note: the process of creating the ADDS takes some time, just have your coffee and wait patiently.
Setup ADDS DNS on vNet
The following message should appear after the ADDS provisioning has completed:
You can check the DNS address by checking its properties:
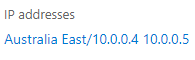
To set these DNS addresses to be used by any VM on the vNet, you can manually copy and set them on the vNet DNS, or by clicking on:
Next, to run the repair , press Fix:
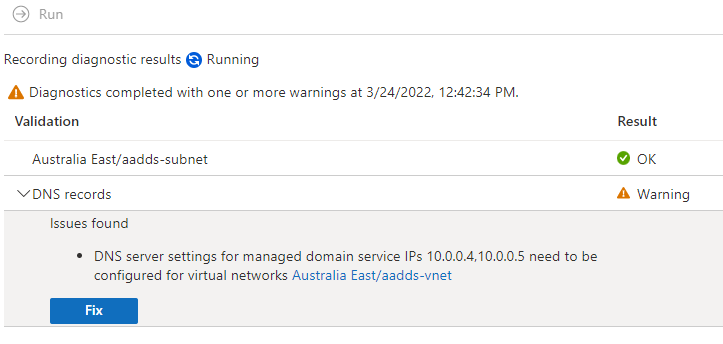
After the repair process has completed, the DNS address is updated on the vNet. We are now ready to provision our Ubuntu Linux Server.
Prepare your Linux VM to join the Domain
Go ahead now and install Ubuntu server 20.04 LTS; next, attach it to the same vNet as the ADDS. After the VM is ready, you can connect using SSH. Now we can start with the following steps:
Note: It might be required that you open the SSH port / 22 on your NSG (aadds-nsg).
- Configure the hosts file to make sure the hostname is correctly configured for the management domain:
sudo vi /etc/hostsOn the hosts file, add the server name and the domain as shown below:
172.0.0.1 ubntsrv ubntsrv.sonaros.ioNote: ubntsrv is the name of my VM, and sonaros.io is the name of the custom domain.
- Install the required packages by running the command in the following screenshot.
Note: When you are asked to provide the “Configuring Kerberos Authentication”, enter your domain (custom) in capitals. In my example, it is SONAROS.IO:
sudo apt-get update
sudo apt-get install krb5-user samba sssd sssd-tools libnss-sss libpam-sss ntp ntpdate realmd adcli- Configure Network Time Protocol (NTP). In your experience with local domains, you know that time is a critical factor when it comes to authentication. To sync the time with the domain, add the domain NTP hostname to the /etc/ntp.conf file.
sudo vi /etc/ntp.confand then add the following:
server sonaros.io- To ensure that the VM is synchronized with the managed domain, the following steps are necessary:
sudo systemctl stop ntp
sudo ntpdate aaddscontoso.com
sudo systemctl start ntp- Join VM to the managed domain. Start by discovering the managed domain name in ALL UPPERCASE
sudo realm discover SONAROS.IO- Then, let’s initialize Kerberos using the
kinitcommand. We use a username that’s a part of the managed domain.
It might be that the following command fails if you do not force the password hash sync by changing the user password. So, before you type the following command, change the user password before continuing. (You can do this by using myapps.microsoft.com)
kinit -V hal@sonaros.ioIf that command above was successful, you can expect to see this line: Authenticated to Kerberos v5
- We are now ready to join the domain. However, from my experience, probably you are going to face an issue with joining to the domain; problems with permissions, etc. After lots of research, I found a quick solution; just add the following line to the sudo vi /etc/krb5.conf and then add the rdns line as follows:
[libdefaults]
default_realm = SONAROS.IO
rdns = false
- Finally, lets join the domain using the following command:
sudo realm join --verbose SONAROS.IO -U 'hal@SONAROS.IO' --install=/The command above takes several seconds to complete. When it has completed, you will have your machine added to the domain – simple.
To test out the success of your steps, see if your Linux VM can connect using a domain username. Try it out with the following command to connect:
ssh -l hal@SONAROS.IO ubntsrv.sonaros.ioConclusion
Adding Linux to ADDS is a very involved process and requires many steps in the right order. After you have made it work once, and can understand the logic behind the steps and the flow, it becomes a very easy and a straightforward process. Obviously, for expediency in this blog post, I didn’t cover any best practices; I provided only the necessary information to get you started. I encourage you to use the following link to learn more: Join an Ubuntu VM to Azure AD Domain Services | Microsoft Docs and to complete the other tasks I skipped.