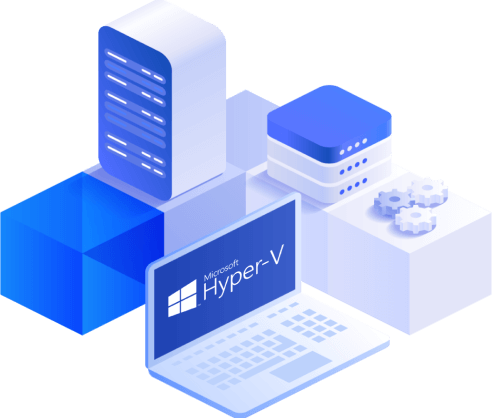
Is there a a faster and more reliable way to deploy SQL environments, it opened the discussion around modern infrastructure design. This article explores how containers are transforming SQL Server deployments through faster provisioning, persistent storage, and production-ready networking.