Many organisations are diverting their focus to protecting their data against Ransomware attacks. Even the best security out there cannot make you 100% immune. So how can you use Azure Private Endpoint to reduce your surface area facing an attack against your data?
Many organisations are diverting their focus to protecting their data against Ransomware attacks. Even the best security out there cannot make you 100% immune. So how can you use Azure Private Endpoint to reduce your surface area facing an attack against your data?
Last week I spent some time discussing and validating several Azure architectures to better secure the backup data as it made its way to the Azure blob storage. Those discussions and validations came about after discussions with several customers and as part of my concerns with one of my own private development projects.
My concerns were raised after I grasped the fact that we can never be 100% secure against malicious attacks; so, my best approach to protecting my data is coming up with ways to minimize the surface area of my backup data facing an attack.
In today’s blog post, I will explain how you can use the Azure Private Endpoint. In the next blog post, I will provide an example of how I incorporated this technology towards better security of my data.
So let’s start with the definition of the Azure Private EndPoint
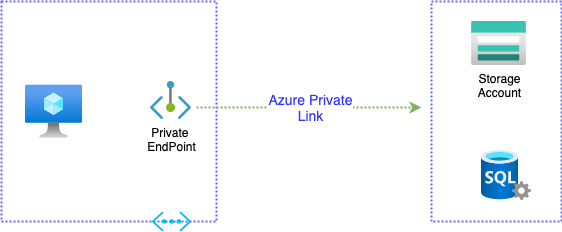
Azure Private Endpoint is a virtual network added to your Azure virtual network. When set up correctly, this newly created virtual network adapter will connect you privately and securely to your Azure service via an Azure private link. The Azure services that can use Azure Private Endpoint are:
- Azure Storage
- Azure SQL Database
- Web Apps
- and more
Architecture
As explained above, when setting up a private endpoint, a new read-only virtual network adapter is added to your virtual network; it is assigned a dynamic IP address from your subnet and mapped to the private link resource. The IP address remains attached and unchanged to the vNIC for the entire life cycle of the private endpoint.
When the endpoint is set up, the connection to the service is carried via the Azure private link while using the private IP.
Summary
Azure Private Endpoint can be used to limit access to the storage account to connections only from the private endpoint and from the Azure virtual network. This can help with the security of your backups data, as we will see in the next blog post. I will take you through the configuration of a private endpoint connection. The good news is that setting up a private endpoint connection is not a complex task, and you can be up and running quickly. There will be more about setting up private endpoint configurations on the next blog post; so until then, stay tuned.
References: https://docs.microsoft.com/en-us/azure/private-link/private-endpoint-overview