Suppose you are going to deploy Veeam Backup for Office 365 on Azure or public cloud, and you want to minimise the surface attack area on your infrastructure? What ports do you have to open, and keep closed, to harden the security of your deployment?
Suppose you are going to deploy Veeam Backup for Office 365 on Azure or public cloud, and you want to minimise the surface attack area on your infrastructure? What ports do you have to open, and keep closed, to harden the security of your deployment?
Ports and Infrastructure
I have been spending some time lately building my Veeam Backup for Office 365 on my Microsoft Azure cloud. The reason behind this exercise came from several requests from Service Providers and customers who want to do the same and need to learn more about the steps. So, I took the initiative and went through the steps to deploy the VBO 365 Infrastructure on Azure. On this blog post I will simplify the process for you, and specify the ports that have to be open between the servers to minimise the security risk of any malicious attack on the infrastructure servers.
To deploy VBO 365 on Azure, I provisioned the following VMs:
- 1 x DC Server
- 1 x VBO Server
- 1 x Proxy Server
* Azure VM Specifications: Standard B4ms (4 VCPUs, 16 GB memory)
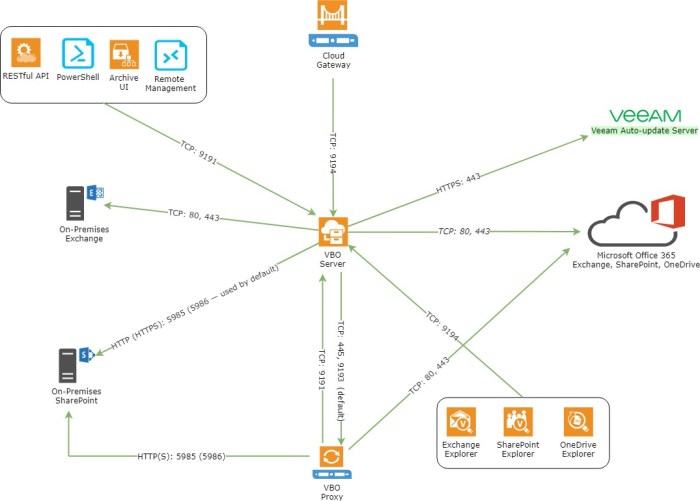
To reduce the risk of malicious attack and secure the infrastructure, I configured the windows firewalls and the Azure Security Groups to accept only the following ports:
Note: The diagram below illustrates the ports that must be open between the VBO servers roles. You can read more about it at this link.
Conclusion
There is not much difference between deploying Veeam Backup for Office 365 on-premises, on Azure, or any other public cloud. The two concerns that customers and Service Providers shared with me was the cost of the storage/repository and security.
On this blog post, I addressed the security and worked on a workaround to use an Azure Storage Fileshares account to be used with Veeam Backup for Office 365. However, at this stage, the workaround I came up with does not completely satisfy the requirement; at least for me. Of course, I will share a better solution as it is develped on a future blog post.