Cloud Backup is not immune to accidental or malicious data deletion activity. Keeping your data offsite is a great strategy to guard against a site disaster or local disaster; but, what if someone compromised your offsite backup by deleting your offsite backup data?
Cloud Backup is not immune to accidental or malicious data deletion activity. Keeping your data offsite is a great strategy to guard against a site disaster or local disaster; but, what if someone compromised your offsite backup by deleting your offsite backup data?
On this blog, I will share a real life scenario I experienced last week with one of our Service Providers. The SP has offsite cloud backup as a service offering.
Scenario
After building the BaaS based on Veeam Cloud Connect Update 3, and successfully onboarding several customers for a trial, one of the tenants become excited about the offsite backup data and he starts simulation data loss and tries to recover from. He had always been able to recover his data from the Cloud Repository without difficulty; that is, until he decided to delete the Veeam Backup Recovery Points from the Veeam Cloud Connect Cloud Repository.
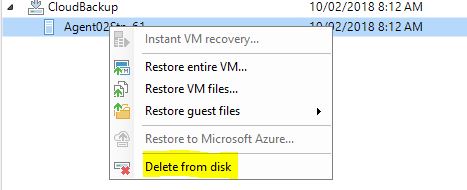
If you delete the Backup Recovery Points, the data will also be deleted from the Veeam Cloud Repository. Our tenant did that and lost his offsite backup.
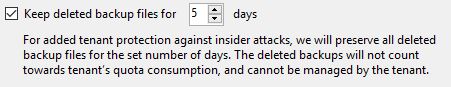
There is good news though. When we went through the cloud backup design and tenant configuration, we decided to enable the new Veeam Insider Protection introduced in the Update 3 release:
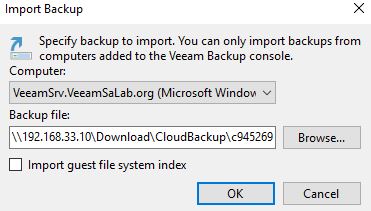
The customer called to discuss the deleted data with the Service Provider, who assured him that the data could be easily recovered. The Service Provider recovers the data from the Cloud Connect Cloud Repository Recycle Bin, and forwards it to the tenant. The tenant imports the recovered data into his backup recovery routine and then carries out a normal recovery.
How Veeam Insider Protection Works
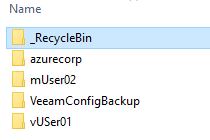
The Insider Protection feature introduced in Veeam Update 3 is designed specifically for the scenario we are discussing here. That is, deletion of the Cloud Repository data by the customer, or anyone with access to the customer infrastructure, either intentionally (maliciously), or unintentionally. On deleting the backup data, Veeam Cloud Connect will move the data to the Cloud Connect Cloud Repository Recycle Bin folder for a specified retention period. The retention period is set during the tenant configuration. (see Figure 2).
If the tenant decides to recover this deleted data, the tenant can contact the Service Provider and request that the deleted data be forwarded to him. On receiving it, the tenant can then use Veeam Import backup to recover from the imported backup points.
Things to be aware of when utilising Insider Protection
- When the tenant backup data is deleted, Veeam will move the deleted files to the Recycle Bin automatically; but, only if “Keep deleted backup file” protection is enabled.
- Veeam Cloud Connect will save only “.VBK” and “.VIB” backup files in the recycle bin. Files of “.VBM” type will be deleted in the process.
- The Service Provider must send the data to the tenant for import locally for the tenant to recover data from the deleted backup files.
Conclusion
In this blog, I discussed how a tenant was testing his offsite backup protection against intentional deletion of the backup files. The same recovery process can be used if you experience a malicious activity that deletes your offsite backup files.
Veeam Cloud Connect will help you and your company to implement an offsite backup strategy. It will help you protect your offsite backup data from any data deletion, including the deletion of the backup files. All it takes is that you ask your Service Provider to enable the new Veeam Insider Protection feature and that you tell them the retention period you want set.